How to Start
So, that´s a really good question and not easy to answer, it really depends on the goals and knowledge you have, but I`ll try to break this down. For a really first start I can recommend the following sources:
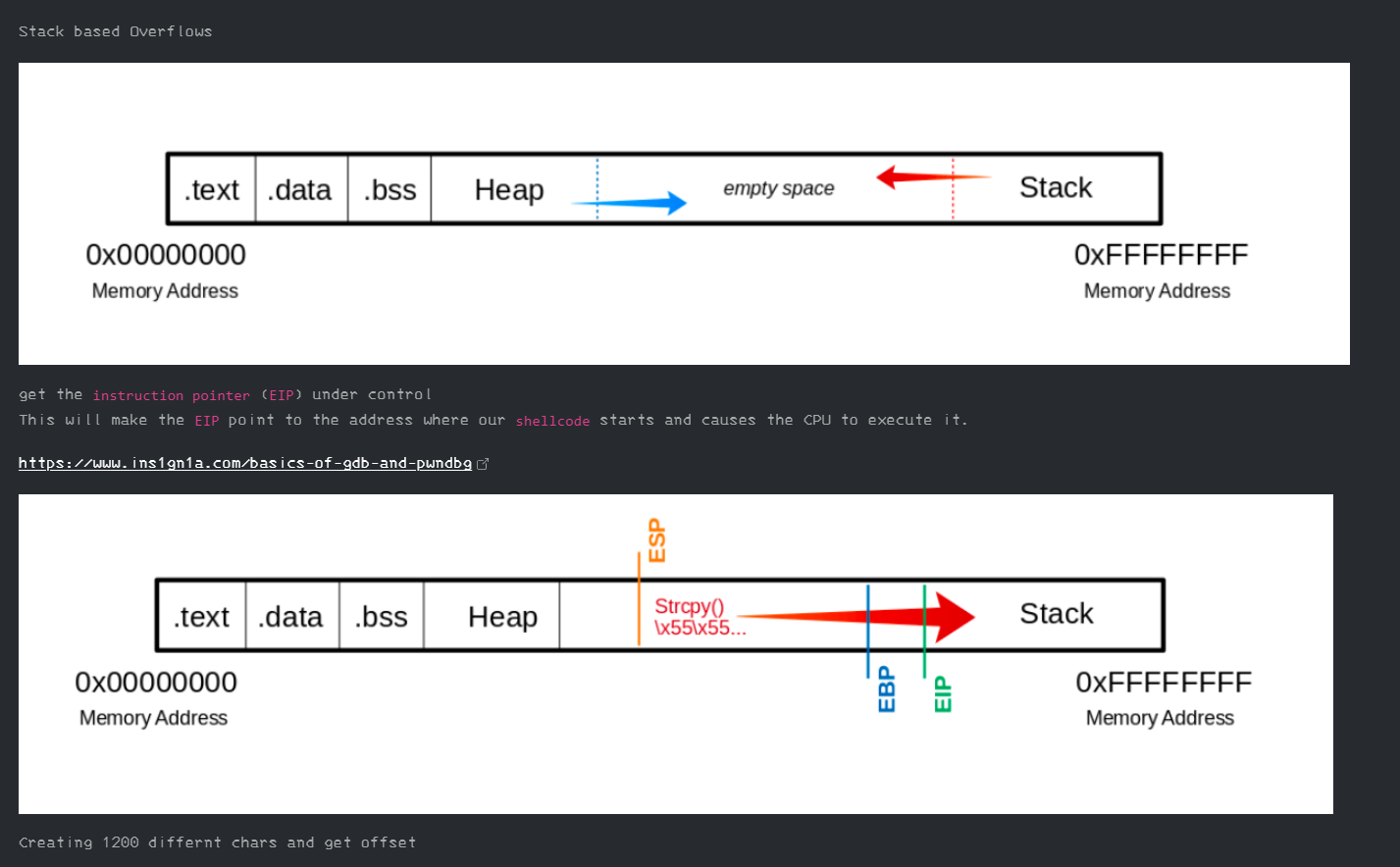
- HTB Academy Stack Based Buffer Overflows
- Cyber Mentors Buffer Overflow YT Series
- TryHackMe Buffer Overflows (Solution)
Also read my other post about Things i wanted to know before i started with Buffer Overflows and follow the Youtube series from LiveOverflow, mentioned in my post.
Assembly Code and Reverse Engineering
The fear… is … big. I know, but if you really want to dive into this topic there is no way around Assembly. I mean for starting with „easy“ challenging BOFs it is not really necessary and you will get better in it by just reading and debugging code but as soon you are facing more complex challenges you need to read and understand Assembly. But, this said, the good point is, this is not what you want or need for the beginning, so I would suggest not to spend too much time in theoretical learning this topic. If you want a starting point I can recommend the HackadayU Reverse Engineering with Ghidra Series, watch them (if you need, more then once) and practice Reverse Engineering and reading C (or P)-Code. Here you can also find some notes about Assembly Basics.
Practicing Reverse Engineer does help, the best place to practice this is crackmes.one (you would know it, if you have done the HackadayU series)
Toolset
There are many tools out there that can help you to get the job done and make your life less painful, but many of them are very similar and switching between tools (meaning you need to learn them) also costs you time. So everybody has his own preferred list, but here is mine and I only can suggest to focus (at the beginning) on you preferred ones.
Ok, but how to learn these tools?
- Ghidra –> HackerdayU Reverse Engineering with Ghidra Series and watching some pros how they use it Reverse Engineering WannaCry
- pwntools –> Cheat Sheet and pwntools on TryHackMe
- gdb –> Basic Commands
- pwndbg –> Basic Commands and Links to Cheat Sheets
Strategy and Tips
Really concentrate on EASY buffer overflows in the beginning, there are many pitfalls out there, a single char or payload miscalculation can change everything and even if everything is correct, you need to fight against broken shells, misbehavior and bugs in the tools or the different python versions (2 vs. 3). So I don`t want to scare you, but BOFs are always a little bit painful and you simple can wast hours on it. On the other hand, these are also very funny and the deeper you dive, the more you would be surprised at what is possible.
Another advise is: don´t spend too much time leaning a single tool or topic, try to learn these tools by completing simple challenges and watch some videos about pwn CTFs. So start with some basic plain gdb and python BOFs and learn to use pwntools und pwndbg asap as they really make your life easier.
Here are also some more good learning sources.
Tutorials
Notes and Blogs
- Basic Fundamentals
- Cheat Sheet
- How to Exploit a Buffer Overflow Vulnerability
- Build An Efficient Pwn Environment
- High level explanation on some binary executable security
Above and Beyond
Well, after learning the basic of assembly, reading and understanding c (or Ghidras) p-code, knowing your tools like pwndbg and pwntools and have done some easy challenges you can think about going further.
One great place to do this is the ROP Emporium. There you will learn how to use some more advanced technics like:
- Building and using ROP gadgets
- writing to process memory
- manipulating chars in the stack or memory
- ret2lib.c
- and so on..
this is also a great place to get more familiar withe the pwntools python framework, which is really handy when it comes to build complex exploits.
If you stuck you can check out CryptoCats Youtube Series or my Notes